SSL, TLS, IPsec, SSH, and PGP are the most popular encryption and authentication protocols that use the SHA-256 algorithm. Linux and Unix also use SHA-256 to secure password hashing, and everyone knows that we get help from the SHA-256 algorithm verifying Bitcoin transactions.
What Exactly is The SHA-256 Algorithm?
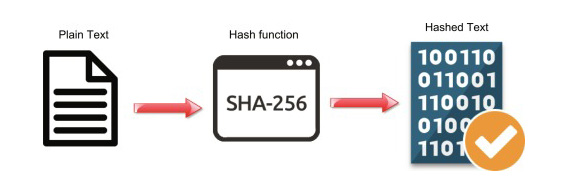
SHA is a modified version of MD5 for hashing data and certificates. A hashing algorithm’s throughput is to make the more diminutive form of the input data in a way that isn’t understandable by using bitwise operations, modular additions, and compression functions.
Simply SHA 256 is a password cracking algorithm, and the mechanism reaches the original data from the encrypted SHA256 output, which we know as the hash. It would only be possible through a trial-and-error procedure in which each combination was singularly investigated, failed, and so on.
Is the SHA-256 Algorithm Secure?
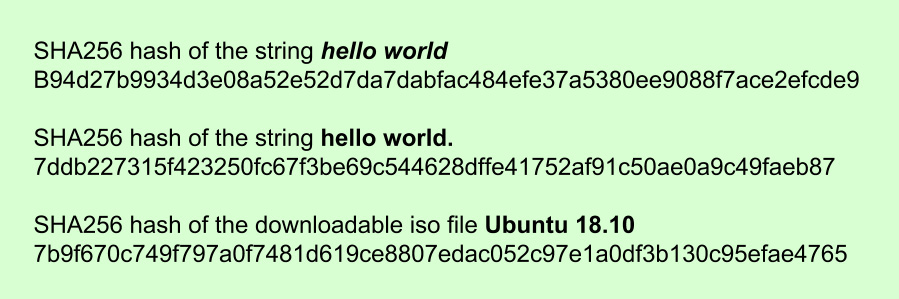
SHA 256 transforms the input data into a value with a fixed length and a virtually irreversible hash value, and we mainly use the algorithm to verify the data’s authenticity. Nothing can crack SHA 256 to data, which makes this algorithm the most secure network in the world.
SHA256 is not an encryption function; naturally, no one can decrypt it.
SHA-256 Algorithm and Crypto Mining
The SHA-256 hashing algorithm takes input blocks of 512 bits (i.e., 64 bytes) and combines the data cryptographically as throughput, and then the result will be a 256-bit (32 bytes) output.
Some of coins we can mine with the SHA-256 algorithm:
BTC, BCH, BSV, BCD, NMC, PZM, XEP, ILC, LCC, UNO, IXC, EMC, BITB, I0C, TRC, ADM, FRC, SWING, SPRTS, SKB, USC, ZET, NTRN, TIT, XJO, EUC, UNIT, GLT, XPY, BXT, 611, EDRC, NKA, PKB, MAY, XCO, DLC, CF, ZYD, TEK, ACOIN, SANDG, XIN, CRE, USNBT, PRM, VEO, BLAST, SAK, ACTN, BSH, BTCV, MIC3, LCNT, QBT, 421 and, IOP.
Conclusion
The SHA256 algorithm is not an encryption function; naturally, no one can decrypt it. It is always 256 bits long, equivalent to 32 or 64 bytes in a hexadecimal string format. Even char (64) instead of varchar (64) would be possible if the sizes don’t change.
